The “Why” of Privacy Metrics
Privacy data analysis falls into three categories: reporting, trends, and benchmarking. For privacy leaders, the value of these operational metrics boils down to two essentials: quantifying program value and managing risk:
Show Me the Money
Since privacy is not a profit center, privacy teams need to quantify their value through data-driven decisions. One privacy professional identified a system configuration as the root cause of a recurring error. By showing the cost of fixing the problem was less than the cost of ongoing incidents, the privacy officer could demonstrate measurable savings.
Reducing Risk
The longer an incident is open, the higher the risk. To manage that risk, a privacy manager may set a goal for closing incidents within a certain timeframe, a metric of special interest to the board as well as security and compliance. Larger organizations with a higher volume of incidents often have a team of investigators on the job. To best manage their team, privacy leaders in these organizations can review each investigator’s turnaround time, their open caseload, and the timeline from incident discovery to notification decision.
Reports: How to Cut Risk and Boost Efficiency with Numbers
Telling the Story Your Audience Wants to Hear
Privacy leaders collect reports for different audiences, such as the board and the operational risk committee. With automation, privacy professionals can filter data to create reports that tell the story of interest to each audience, whether that’s a particular category of incidents, a line of business, or specific time period. And the more data you can gather the better. Often, helpful patterns may emerge only after you’ve collected a sufficient amount of information.
What Will We Work on Today?
Reporting also helps with privacy initiatives. One privacy team tracks incidents based on the specific data elements they consider to be sensitive information. With this insight, they identified two channels where the majority of incidents involving sensitive information occur. The team launched initiatives to eliminate or reduce the amount of sensitive information in those channels and therefore limit exposure in the event of a privacy incident.
Focus on One Thing at a Time
Reporting drives efficiencies. You can use metrics to track how long your team spends on each stage of incident response, such as investigation or remediation. If the numbers show that a member of your privacy team is more efficient at a certain stage, they can share best practices. Automating the different stages can cut response time, helping privacy pros meet even stricter regulatory timelines. Finding ways to streamline the different steps within each stage will streamline the entire process.
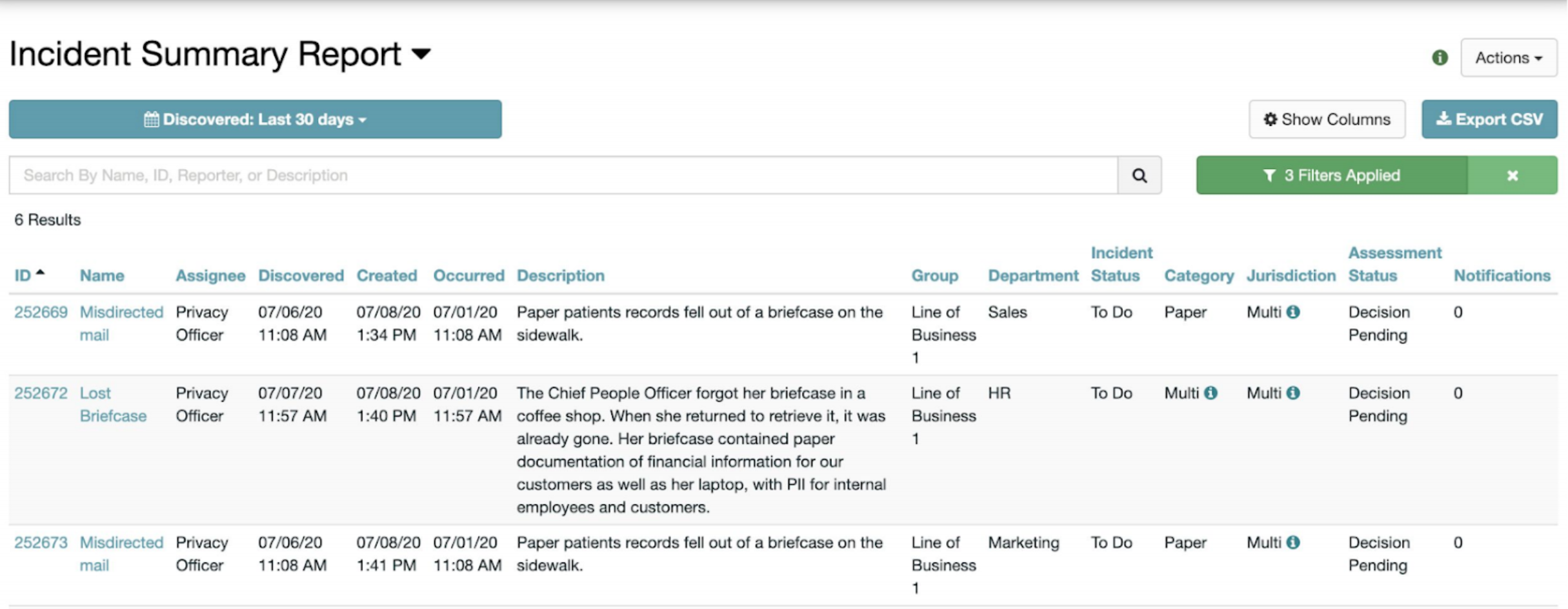
Want to Cut Risk? Answer the Basic Questions
Reports, such as an incident summary report, answer important questions in privacy’s daily quest to manage risk: How long has an incident been open? Is there a risk of missing timelines? Tracking notifications helps privacy ensure they’re meeting reporting obligations and avoid delays in providing notification.
Trends: How to Identify Root Causes and Remediate Risk
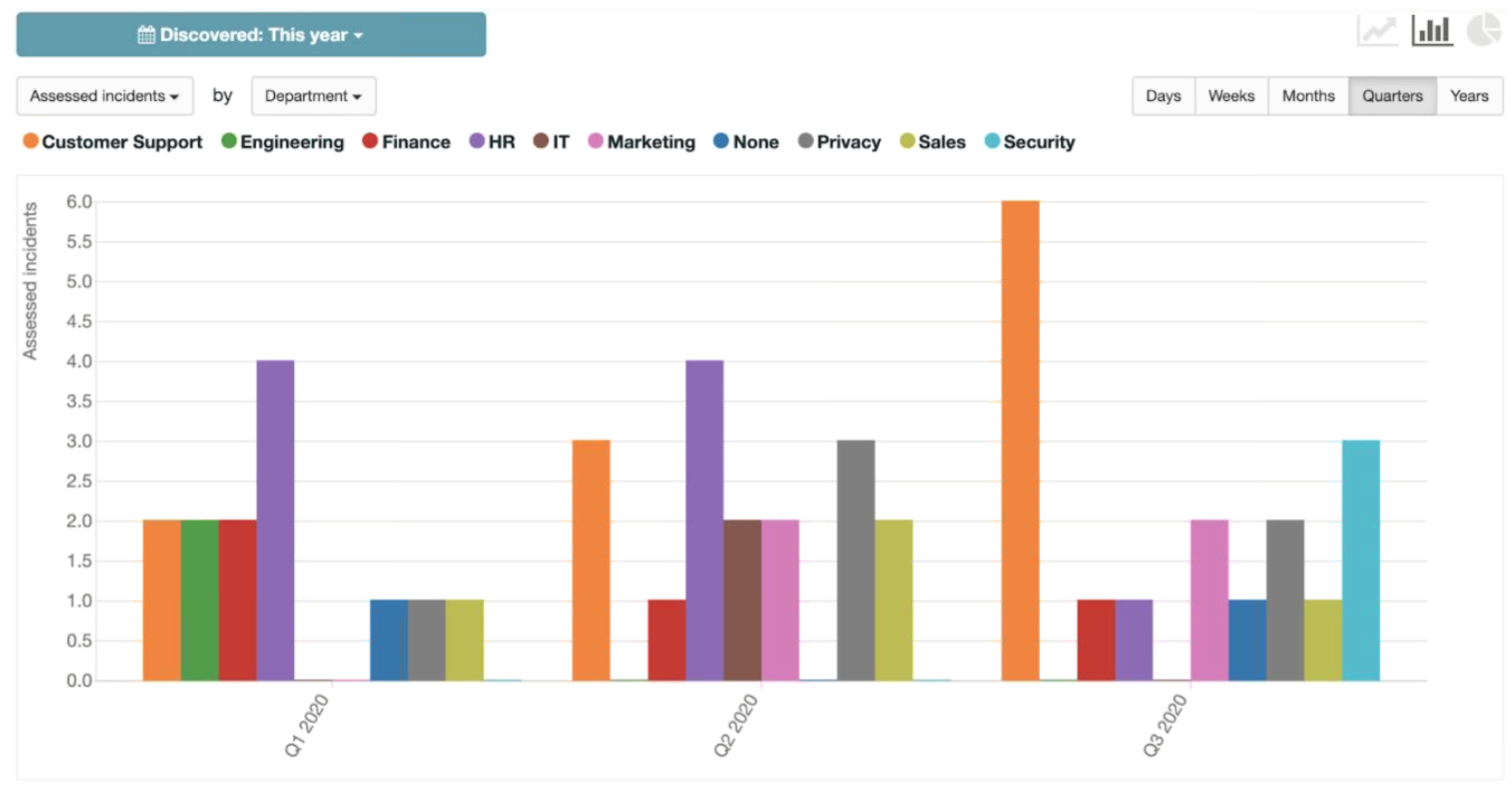
Reports are valuable, but as Nick Church, RadarFirst’s software engineering manager and moderator of the Deep Dive virtual session, pointed out, trends are more fun. Privacy trends, which are a summary of information over time include both volume and efficiency metrics:
Volume
- Number of incidents
- Percentage of notifiable incidents
- Size of incidents (# of affected individuals)
Efficiency
- Median time to detection (MTD): Time from occurrence to discovery
- Median time to privacy response (MTPR): Time from discovery to privacy risk assessment
Look for Patterns
Trend data measuring the volume of incidents often reveals important patterns that can guide privacy initiatives. For example, a privacy team may identify a spike in incidents in a department during a particular timeframe. One of the privacy leaders in the session shared how his team annually ranks the different areas of their organization from high to low. The top three are prime candidates for remediation. These departments will receive statistics on the numbers and types of issues they’ve had for the past three years, and suggested plans for remediation. With privacy, these departments will track their improvements — an incident report card.
Tracking Incidents by Type Improves Accuracy
To measure efficiency, privacy teams evaluate metrics such as the median time from discovery to privacy response. But different incident types take different lengths of time to resolve, so lumping them all together can skew results. A best practice is to classify incidents by category to better identify specific areas of improvement. Say you notice a trend identifying a higher number of incidents that are due to misdirected mail, and launch a training program to educate your staff on correct procedures. A downward trend after the training provides demonstrable proof that your initiative works — and you can justify the cost of additional trainings to further reduce risk.
Benchmarking: Learning from Your Peers
To help privacy teams assess their operations, RadarFirst created its inaugural benchmarking report, which compares important metrics across peer industries. This report is full of insights gleaned from a rich set of aggregated metadata that organizations can learn from. Here are four key benchmarking metrics included in the report (note: In the Radar platform, organizations can compare their specific metrics to those of their peer industries across these four benchmarks):
- Percentage of notifiable incidents, which is the number of assessed incidents with at least one ‘Yes’ decision to notify individuals divided by the total number of assessed incidents in the time period.
- Percentage of on-time notifications, which is the number of notifications where the ‘date notified’ is after the calculated due date divided by the total number of notifications with a decision of ‘Yes’.
- Incident category breakdown, including % of total incidents that are electronic, paper, and verbal or visual
- Incident Timelines, from discovery to notification decision
Financial Benchmarking
To protect consumer financial privacy, financial services organizations must adhere to the Gramm-Leach-Bliley Act (GLBA). Benchmarking data reveals a much higher rate of notifiable GLBA incidents compared to overall incidents, likely because regulators who issued guidance on GLBA set a lower notification threshold. Therefore, what may not constitute a notifiable incident under state laws might require notification under GLBA in certain circumstances.
Healthcare Benchmarking
Similar to GLBA, the rate of notifiable HIPAA incidents is higher than notifiable incidents overall. However, the rate of on-time HIPAA notifications is also higher than overall incidents. One healthcare privacy leader cited the usefulness of benchmarking on-time notifications to assess performance — whether that shows room for improvement or that “you’re doing the right thing.”
Privacy metrics show your strengths and your weaknesses
Strengths reveal best practices you can apply across your organization (and prove ROI), and weaknesses pinpoint where to put your time and money. So measure, measure, measure, and don’t be afraid of the results. We’re all learning, and we can all learn from each other.

