What Does it Mean for Privacy and Security Professionals?
Last week, the Office for Civil Rights (OCR) announced the first ever enforcement settlement for lack of a timely breach notification – a fine of $475,000 for Presence Health, a large healthcare network serving Illinois. In the course of investigating the breach, OCR determined that Presence Health had “failed to notify, without unreasonable delay and within 60 days of discovering the breach, each of the 836 individuals affected by the breach, prominent media outlets (as required for breaches affecting more than 500 individuals), and OCR.”
What does the latest enforcement action mean for HIPAA regulated entities? This enforcement should not have come as a surprise, as OCR placed emphasis on compliance with the Breach Notification Rule when it launched its Phase 2 audit program. Unlike the Phase 1 audit program, where much of the emphasis was on auditing compliance with the security rule, Phase 2 was a clear signal to the industry that OCR expected covered entities and their business associates to comply with Privacy and Breach Notification Rules. Below are three major takeaways.

Time is of the Essence: Streamline Incident Response to Avoid Missed Notification Deadlines
When it comes to notifying the regulators, and affected individuals in the event of a data breach, time matters. From discovery date to investigation and a multi-factor risk assessment for making a breach determination, many privacy and security professionals find themselves racing the clock to compliance.
There is no such thing as “too late” when it comes to OCR – even if you’re late in reporting, you still must report. In OCR’s announcement of the enforcement settlement, it was specifically stated that “OCR balanced the need to emphasize the importance of timely breach reporting with the desire not to disincentive breach reporting altogether,” referring to both the amount of the fine, which is certainly significant but not prohibitively huge, and in the corrective action plan that outlines a path forward for Presence Health.
{{cta(‘3139d24c-9c33-40f6-a735-d8be26b44c23′,’justifycenter’)}}
As soon as an incident involving PHI is discovered, the incident response team must have a clear and streamlined process for escalation, documentation, and ultimately performing a multi-factor risk assessment to make a breach determination. “The settlement reinforces the importance of having a written – and actionable – incident response plan,” writes Christopher G. Cwalina and Shannon Harsfield Salimone of Holland & Knight, LLP. “Having a written plan in place helps to organize and streamline the incident response process.”
Lateness in notifying OCR can also have a snowball effect when it comes to the ultimate cost to your organization.“Namely, the cost of actually providing the notice could be compounded by a fine for sending the notice too late.” according to Matt Fisher, chair of Mirick O’Connell’s Health Law Group and a member of the firm’s Business Group.
Looking Good on Paper Means Keeping Track of Paper Incidents
One item of note in this data breach was that the breach involved the loss of paper-based records. Jean Tomasco, in Data Privacy and Security Insider, also expressed surprise in this fact, writing, “Interestingly, the breach stemmed not from a cyber-attack but from the loss of paper-based operating schedules.” Why is this detail worth noting?
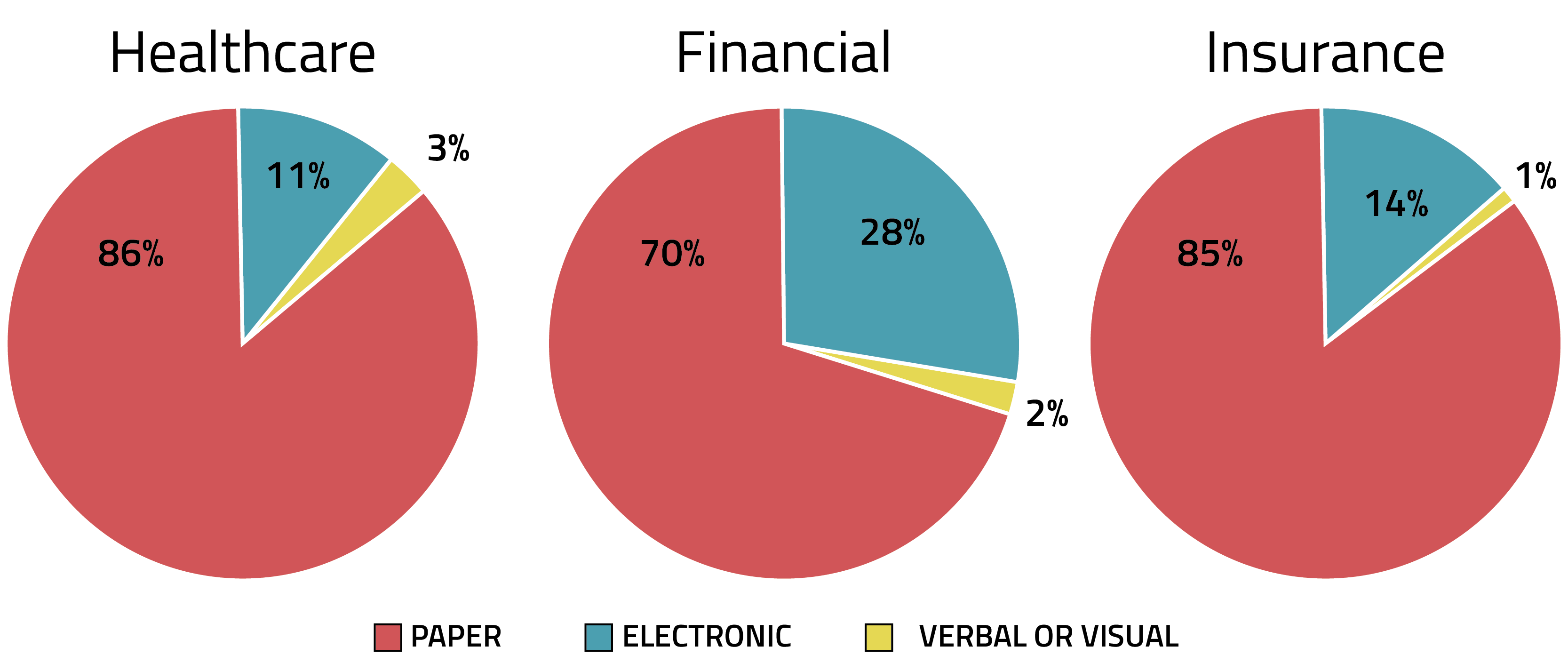
There is a common misconception in incident response that electronic incidents and breaches are more prevalent than paper. In reality, while electronic incidents may typically expose more records per incident, paper incidents are far more commonplace. Analyzing incident metadata from RADAR shows that, across three major industries dealing with regulated data, the majority of data incidents are paper related:
In this case, paper-based operating schedules that included PHI of 836 patients at Presence Health were compromised. OCR requires notice of both paper and electronic data breaches, and many US states are beginning to expand their data breach notification laws to include paper in addition to electronic data – see Rhode Island’s new data breach notification law enacted last year, for example.
Expect Continued Activity from OCR in 2017
The recent enforcement settlement comes after a year of bold moves from OCR in 2016 with regard to HIPAA violations, including newly issued OCR guidance on cloud computing, and ransomware, as well as the launch of the Phase 2 HIPAA Audits program. In 2017, OCR’s experienced staff is likely to continue this momentum pending the appointment of a new agency director. We can anticipate seeing further breach notification enforcement from OCR, and OCR has already announced a plan for limited onsite HIPAA audits this year.
For privacy and security teams looking to develop and maintain a culture of compliance, the best action you can take now is to clearly define your incident response plan, assign roles, and practice regularly, and learn the 8 steps to OCR Audit compliance, before an incident has occurred.
Related Reading:

