- Incident identification
- Investigation
- Assessment
- Decision of whether or not to notify
- Periodic analysis to improve the process
So, what makes privacy incident response so complex, and what can we do to simplify it?
We tackled that topic in a recent Privacy Collective session, with Rachel Reid, VP, Chief Counsel & Chief Privacy Officer at the American financial services company Voya. Reid summed up the complexity in two words: “It depends.” Quite simply, each incident, organization, industry, and jurisdiction is different, and the combination of so many factors means there is no cookie-cutter approach. That said, the more consistent and repeatable your privacy incident response process is, the more efficient and successful you’ll be in dealing with the complexity. Let’s look at some factors and solutions.
The Steep Path to a Data Breach Notification Decision
 The first piece of good news is that not all phases of incident response are equally difficult.
The first piece of good news is that not all phases of incident response are equally difficult.
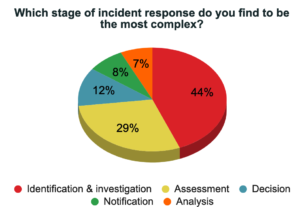
When we asked Privacy Collective members which response stages are most complex, it was clear that the up-front work is the hardest:
- 44 percent cited the incident identification and investigation stage as most complex
- 29 percent named the assessment stage
Reid agreed with those rankings in general: “Once you’ve identified and assessed your incident, making the notification decision and notifying usually isn’t that hard.”
But she cautioned that isn’t always the case.
“If you ask me which of the first stages is the most complicated, I’ll give you a typical lawyer’s answer: ‘It depends on the incident.’ Some have very confusing facts, or there are a lot of facts, or the facts are difficult to discover.”
“Maybe the facts change as your investigation goes on. Sometimes you need to bring forensic experts in and technologists to figure things out. Other times you can also have an incident where the facts are pretty clear and well known, but there are a lot of gray areas where you have to use your judgment in order to match the facts to the laws of whatever set of jurisdictions apply.”
Investigating an Incident: Privacy Takes the Lead
When a privacy incident is identified, there are many levels of questions that demand answers.
The Basics:
- What happened?
- When, where and how?
Data Security Questions:
- Is there a security gap we need to close?
- What can we still do to mitigate the risk?
Regulatory Questions the Privacy Team Must Answer:
- What data was disclosed?
- Were there any data protection measures in place?
- Are we a data controller, processor, or service provider in this situation?
Reid finds that the hardest part of the identification and investigation stage is the dependence on other people and groups.
“As privacy professionals, we are highly dependent on others to complete the first stage. I’m not the one who can look at the logging and figuring out ‘Did bad guys get in? What did they see?’ But we’re the ones with the notification deadlines, so we really want to get all the data quickly so we can move on to assessment.”
Reid says two practices have helped her team succeed with this phase: having a single point of incident intake and having privacy in charge.
Because Voya had been spun off from another company (Dutch company ING sold off its US business in 2012), Reid had an opportunity to recreate the company’s incident response process.
“We learned that we had to have a single intake point for privacy and security incidents. Otherwise, it becomes absolutely impossible to manage and triage and comply with timelines. We also learned that you have to reinforce that intake method with your staff, whether you use a shared email box or an application or you encourage people to pick up the phone. Whatever your process is, you want everything reported as quickly as possible and through a single source.”
Reid also says, because privacy is responsible for compliance, privacy needs to manage the investigation process.
“We have 6,500 employees and over 13 million customers, so we get multiple reports a week. I have to be able to quickly gather enough facts to say, ‘This is a big deal and we need all hands on deck.’ or ‘This is most likely not a notifiable incident and we can take a little more time sort of gathering details.’ You need an effective triage system, and you need to clearly understand who is leading the process.”
“Where I’ve seen the ball drop or timelines missed, it’s been because it’s unclear who is giving the orders. In our organization we’ve said, if there is a potential privacy incident, the privacy office is in charge. Then, from the start, you can be collecting the facts in the way the privacy team needs, so they can determine notification obligations in time to meet all the reporting requirements.”
Making Incident Assessment Thorough and Consistent
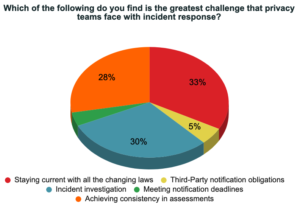 The biggest privacy incident assessment challenge for Reid’s organization and for many other Privacy Collective members, according to an online poll, is keeping up with and applying all the relevant laws and regulations from multiple jurisdictions.
The biggest privacy incident assessment challenge for Reid’s organization and for many other Privacy Collective members, according to an online poll, is keeping up with and applying all the relevant laws and regulations from multiple jurisdictions.
See how Radar’s Breach Guidance Engine works >
She says that problem is multiplied because of different data sets for operations in each state, territory, or country. “Fortunately, I haven’t had to manage many incidents where there were potentially thousands of impacted individuals. But think of some of the large breaches in recent years that affect millions of people, then consider that data elements may be different for different people.”
“Some might have had a passport number in that database. I might have a driver’s license number and others don’t. We have the states out there like North Dakota where exposure of just the name and date of birth will trigger a notification obligation. So, we have many people with many different data elements, then Voya is looking across all 50 states and Puerto Rico to figure out notification requirements.”
“When we’re doing an assessment, I envision it as a deck of cards, and I’m making different stacks. This group is people in California, and they have Social Security number and passport number. This one is Maine, and they only had contact information.”
“You have to parse it out, make sure you have your facts straight, and make sure which individuals fall into which bucket. And then you apply applicable law or laws because in some states, such as Connecticut, you might have a state breach notification law, but then you also have the department of insurance requirements, which are different.”
Stay up to date with global data breach notification regulations using Breach Law Library >
Another factor in assessment is the risk question: are you over- or under-notifying?
“In 2009, when we saw the first privacy laws, people were of the mind ‘Let’s just notify everybody. There’s no harm.’ Then we realized the costs and risks of over-notifying, so now we decide for each jurisdiction, and that can be subtle.
There might be a one-word difference between state laws. Is the notification obligation triggered by access to personal information or by acquisition of personal information? That’s a very material difference. Add that factor to your incident facts, your high number of people, your different data elements, your different states, and how do you map that out so you can make the right decision for each individual?”
Notification Decisions: The Consistency Challenge
The goal of the decision phase is not only to make data breach notification decisions, but to make consistent ones.
Reid asks, “If there’s a gray area, how do you get certainty that you’re applying the law the same way every time, when it’s based on a set of facts that is going to be different every time? And how can you be sure you are doing it in a similar way to peer companies in your industry?”
“If 90% of the industry notifies when you mis-mail a piece of paper that has a Social Security number printed on it and you don’t, that’s something that’s going to stand out to a regulator. The more you can fit yourself neatly in the middle and be consistent with yourself and with what others are doing, the better off you’re going to be.”
Reid’s team at Voya has automated their incident response process using Radar, and that has helped them to make more consistent decisions and to document their decisions and exceptions. It has also helped them identify third-party notification obligations that apply to a privacy incident.
“We provide financial products for employer groups, so, we have contractual notification obligations to very large institutional clients whose employees are purchasing retirement products or employee benefit plans. I think every sophisticated company is insisting on breach notification language in their contract, and some of it is very detailed as far as when you notify, who you notify, how you notify, and what should be included there. That has to figure into your notification decisions.”
Ask for the Help and Tools You Need
Reid admits that the complexity of privacy incident response is an ongoing challenge and consistency is an ongoing quest. But, she says, “If you take the time to really map out your process and then follow it every single time, I think that’ll get you as close as possible.”
“Sometimes you need outside forensic firms to help you investigate. Sometimes you need outside counsel because you’ll have to make a tough judgment call and you won’t know what other people have done in similar circumstances. And sometimes it’s a technology tool to help intake your incidents, to triage and assess them, to track them and do your reporting. Something that’ll make nice, colorful reports with all the relevant information that your management wants to see.”

