Securing budget may always be an uphill battle, but the relative grade of that path will ease when decision-makers understand the value of privacy programs. To learn how different leaders are approaching that effort, The Privacy Collective team talked to Rosemary Morgan, Chief Privacy Officer and Leader of Compliance Programs at Brighthouse Financial, and Patricia Thompson, AVP Compliance and Deputy Chief Compliance Officer at Pacific Life, in a recent virtual session entitled “Quantifying the Value of a Privacy Program.”
The Cyber Security/Privacy Budget Paradox
In most organizations, privacy program budgets pale in comparison to cyber security budgets. Yet, anonymized 2018 and 2019 data from RadarFirst customers shows that over 98 percent of incidents are unintentional, caused by human error, not theft or cyberattacks. And even cyberattacks are often made possible by human error, such as responding to phishing campaigns—the kind of errors that privacy programs can help educate against. So, what gives?
Morgan believes the budget disconnect lies in a lack of understanding:
 I think people have a better idea of IT security. ‘That’s my computer, and people can hack into it and steal things.’ Privacy is a bit harder to wrap your head around. That’s a reason to collaborate very well with your security colleagues, because often they have more funding.
I think people have a better idea of IT security. ‘That’s my computer, and people can hack into it and steal things.’ Privacy is a bit harder to wrap your head around. That’s a reason to collaborate very well with your security colleagues, because often they have more funding.
Thompson emphasized that privacy needs and deserves a stand-alone budget:
“I’m still surprised, when running through reported incidents, how often something identified by cyber security is really privacy, yet the cyber team has an ever-expanding budget and the privacy team gets a smaller chunk. It’s because many people don’t understand the distinction between the two programs.”
A Private Education
Morgan and Thompson say it’s critical to educate stakeholders and decision-makers on what privacy programs do. Morgan recommends showing what happens in the absence of a privacy program. The news is full of mishandled breaches, with the huge potential for reputational damage. Then there’s the complexity:
“When I explain that there is no federal law that governs breach notification, I get the big eyes. When they understand the ever-changing compliance and threat landscape, what’s involved in evaluating and determining whether notification is required in all those states, and that it’s never ‘business as usual,’ that brings a level of respect and understanding that we didn’t previously have.”
Thompson’s privacy teams worked to educate peers and decision-makers about the distinctions between privacy and security:
 We have detailed RACI documents that delineate the different responsibilities and lines of authority, showing how we add value that is different than the cyber security value. They are really useful in justifying our stand-alone budget.
We have detailed RACI documents that delineate the different responsibilities and lines of authority, showing how we add value that is different than the cyber security value. They are really useful in justifying our stand-alone budget.
She also appeals to her colleagues’ personal experience:
“We are also all consumers who want our information protected, as well as employees responsible for doing the protecting. When we drive home the personal nature of the information, it does resonate with our employees. When they see how business and consumer interests are aligned, it helps to propel the program forward.”
Evolving Use of Metrics
Both Morgan and Thompson say that metrics are the foundation of their programs and their budget arguments. The process starts with choosing the right metrics to drive change. Thompson says:
“We’re constantly evolving what and why we measure and how we report it out to different audiences. In a privacy program, it’s often the metrics of absence that show our biggest and best value: the absence of incidents, the absence of regulatory reports, the absence of inquiries. But we also use positive metrics that show collaboration, cooperation, and consistency. ‘Are we treating people in the same category in the same way? Are we meeting expectations?’ We win support from the business when we can show a consistent, logical approach that our consumers appreciate.”
Morgan says metrics are also valuable from a resource allocation perspective:
 All our teams are small, so metrics can support the argument for additional headcount, or they can justify software to help with incident response, as we did to bring in RadarFirst. We can show that software would free up a person’s time to do something else they need to do. Metrics have been extremely valuable in justifying those acquisitions.
All our teams are small, so metrics can support the argument for additional headcount, or they can justify software to help with incident response, as we did to bring in RadarFirst. We can show that software would free up a person’s time to do something else they need to do. Metrics have been extremely valuable in justifying those acquisitions.
Thompson says headcount was also the impetus for metrics in her organization. But as they brought on tools such as Radar to assist with metrics, they were able to evaluate their overall program in more depth:
“For example, we all suspected we had been under-escalating and under-reporting incidents in pockets. So, the metrics have been really helpful in validating the program and its efficiency.”
Privacy Programs Built on Relationships
Thompson says communication and relationships are the final key to showing the value of privacy programs:
“We show peers and senior leadership how privacy is a customer expectation, and how it helps build our brand in meaningful ways. We also highlight how we partner with the business, helping them accomplish the things they want to accomplish.”
Strong relationships with business managers get the privacy team a seat at the table in the early stages of a project, so the project isn’t hampered by regulatory issues down the line:
It helps us to build privacy in early rather than trying to bolt it on,
and it leaves them with a positive experience of us.
Morgan adds, “Communicating with those groups and breaking down barriers is even more paramount during the pandemic, when we’re remote and we can’t just knock on the door. I encourage employees and stakeholders to speak up proactively and say when something’s off. For the time being, I would say to over-communicate!”
Side-Effects and Opportunities
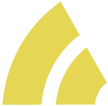
 Ironically, the coronavirus seems to have had positive side effects for many privacy programs. In an online poll, 85% of respondents felt the last few months have increased the value of the privacy team within their organizations. Thompson says the shift to remote working has brought her program more visibility, as the privacy team has worked with other functional areas on identifying not only new privacy processes but new risks and shifts in consumer expectations. Morgan says her team has distinguished itself by proactively planning for an eventual return to the workplace:
Ironically, the coronavirus seems to have had positive side effects for many privacy programs. In an online poll, 85% of respondents felt the last few months have increased the value of the privacy team within their organizations. Thompson says the shift to remote working has brought her program more visibility, as the privacy team has worked with other functional areas on identifying not only new privacy processes but new risks and shifts in consumer expectations. Morgan says her team has distinguished itself by proactively planning for an eventual return to the workplace:
“We’re already thinking about things like taking temperatures and storing that information. All of those things have brought privacy to the forefront and made us more visible.”
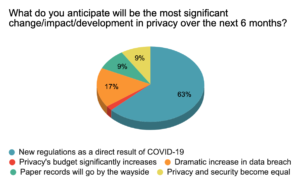 That enhanced visibility is likely to continue: 63 percent of respondents to a third poll expect new privacy regulations as a result of COVID-19, and 17 percent expect a dramatic increase in data breaches as a result of virus-related disruptions.
That enhanced visibility is likely to continue: 63 percent of respondents to a third poll expect new privacy regulations as a result of COVID-19, and 17 percent expect a dramatic increase in data breaches as a result of virus-related disruptions.
With increased visibility and growing privacy challenges, now is the time for privacy program leaders to make the case for the resources they need. So, here’s a statistic for your budget justification toolkit: A recent Ponemon study found that preventing a single cyber attack saves an average of $682,000, yet cyber security managers said only 18 percent of their budgets are spent on prevention. If awareness training provided by the privacy program prevents one or two cyberattacks per year, how much of your budget would be justified by that alone?
Good luck!
If you want to attend upcoming online sessions, receive new content, and network with colleagues about privacy challenges, you can join The Privacy Collective here.

