Regulatory Risk Management, Simplified.
Replace manual reviews with intelligent automation that identifies obligations, documents compliance, and builds efficient programs.
Confidently Navigate Regulatory Risk with Intelligent Automation
The Radar® Risk Management Platform replaces manual, subjective risk assessments with patented automation to guide your team to compliant reporting decisions. Simplify the complexities of AI risk requirements, privacy and security data breach laws, and third-party contractual obligations so your team can act swiftly and maintain compliance at scale.
Proactive Compliance in a Changing Landscape
Regulations change but your playbook shouldn’t. RadarFirst equips privacy and compliance teams with intelligent, proactive workflows that reduce risk, automate audit documentation, and effectively manage regulatory shifts.
Minimize Risk
Assess and resolve regulatory and contractual risks using integrated legal guidance. RadarFirst enables you to swiftly identify and review relevant laws, policies, and obligations, allowing your team to act with speed and assurance, rather than relying on guesswork.
Ensure Compliance Documentation
With RadarFirst, every incident and decision are thoroughly documented, guaranteeing that your compliance processes are precise, consistent, and ready for audits across all jurisdictions—from HIPAA to GDPR to DORA and more.
Boost Efficiency
Eliminate manual reviews and improve incident response with scalable automation. RadarFirst simplifies processes, helping your team create effective, resilient programs that grow with your business.
Featured Resources

2025 Privacy Incident Management Benchmarking Report

EP 04: Keeping up with the SEC | On Your Radar Podcast

RadarFirst Investigates | SEC Rules: Cyber Management
Industry-Specific Compliance, One Powerful Platform
Schedule a Demo
Chosen by Industry Leaders
Frequently Asked Questions
“Materiality” is based on each organization’s unique definition of risk. In order to determine an incident’s capacity for material harm, each organization must first have a working process to categorize severity thresholds for which to qualify each incident and how they’ve involved stakeholders in the decisioning. From there, assessing the materiality of an event is a matter of determining what tangible impact the event may have on business operations and whether they’re substantial in the eyes of regulators, stakeholders, or investors.
Learn MoreA security incident is a scenario where there is an unauthorized disclosure of PII. For example, an attempted phishing attack or social engineering attack. A data breach is when that incident is notifiable under breach
notification laws. While all data breaches are privacy incidents, not all incidents are breaches.
- What are some examples of a non-breach event?
- Some examples of an event could include a security event that required response and reporting to your Board but contained no PI, or learning about a compromised server that is found to contain encrypted data.
- What are some examples of a privacy incident?
- Some examples of a privacy incident can include: a laptop containing PII is stolen, an email with PII is sent to the wrong person, or a box of documents with PII is lost during shipping.
- What is a security incident under GDPR?
- According to the GDPR, “a breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorized disclosure of, or access to, personal data transmitted, stored or otherwise processed.”
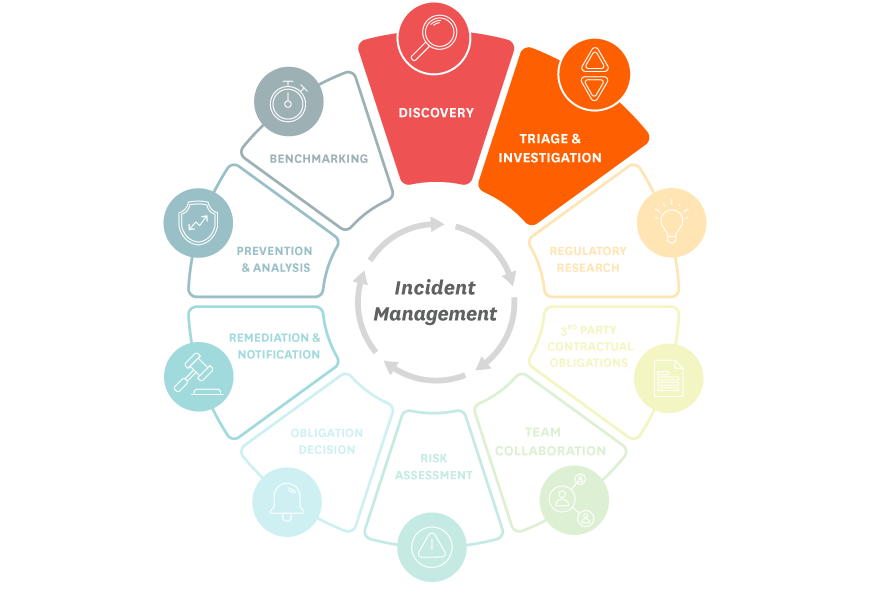
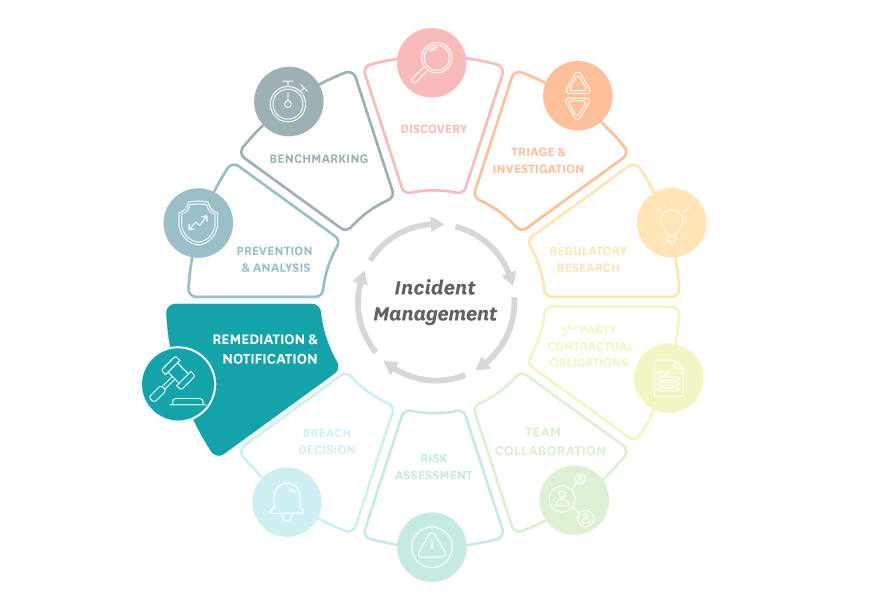
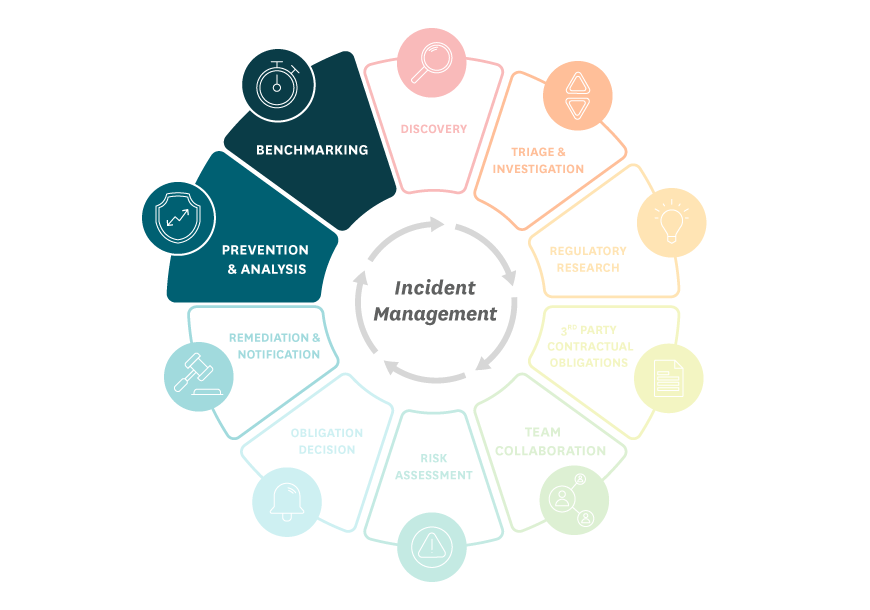
A successful privacy program should simplify the incident management lifecycle to reduce risk for your organization and build trust for your brand. The program should help your team arrive at consistent and reliable breach decisioning every time. A mature incident management program should be intelligent – capable of automatically mapping the regulatory landscape and agile, to stay ahead of all relevant laws.
Our onboarding timeline ensures that your team launches feeling confident and empowered, without taking time and resources away from other priorities.
During your onboarding experience, your dedicated specialist will guide you through customization and configuration options, best practices, and help bring your digitally transformed, privacy automation to life.
Learn MoreRadar® offers established integrations with preferred security and compliance providers, like ServiceNow, Splunk Phantom, Protenus, Fair Warning, and more.
Additionally, a robust and agile API streamlines the connection between data detection tools and Radar®.
Learn MoreThe Radar® platform is designed, built, and supported with security and privacy in mind.
We understand the unique responsibility that we have as we help you simplify incident management. We need to meet the same obligations that you must meet, and you depend on us to be trusted stewards of your data and your reputation.
Learn More