Data Breach Notification: How to Assess Your Incident Risk Assessment
Jump to Section
Highlights:
- Less than 7% of privacy incidents are notifiable. How does your notification percentage stack up?
- 4 tips to find the cause of over- or under-notifying
- The 7% solution: make the right choice about notifications
The million-dollar question in Privacy: How accurate is your organization’s incident response in determining whether incidents are notifiable? In fact, depending on the size of the incident and the jurisdictions involved, it’s much more than a million-dollar question.
According to the latest Ponemon Institute Cost of a Data Breach Report, notification costs now average $150 per record, so one or two incidents involving a few thousand people can quickly add up. And failing to meet regulatory notification deadlines can incur high penalties, such as GDPR fines up to $22.07 million or four percent of annual revenue, whichever is greater. Plus, over-notification can create the impression of poor privacy practices with both regulators and the public.
The goal of privacy incident risk assessment should be to ensure compliance without overspending on notification. And with privacy regulations and regulatory guidance changing constantly, that’s quite a balancing act. One way to help keep your footing is to compare your organization’s notification rate against industry benchmarks, then use your internal metrics to pinpoint problems.
Level Set: What Percent of Incidents are Notifiable?
Since 2018, RadarFirst has been publishing incident response benchmarks based on statistics from our incident response management platform. These studies have consistently found that, across all industries, less than 7% of incidents turn out to be notifiable. Note: if 7% seems low, that’s because these figures are aggregated from Radar user metadata. Users of the Radar incident response platform leverage an intelligent incident response solution, decentralized incident intake forms, and privacy industry best practices.
While there is slight year-to-year variation, these numbers have held steady despite new regulations such as GDPR and CCPA coming into effect, expanded definitions of personal and sensitive information, and the disruption and new privacy risks introduced in 2020 as workplaces went remote due to COVID-19.
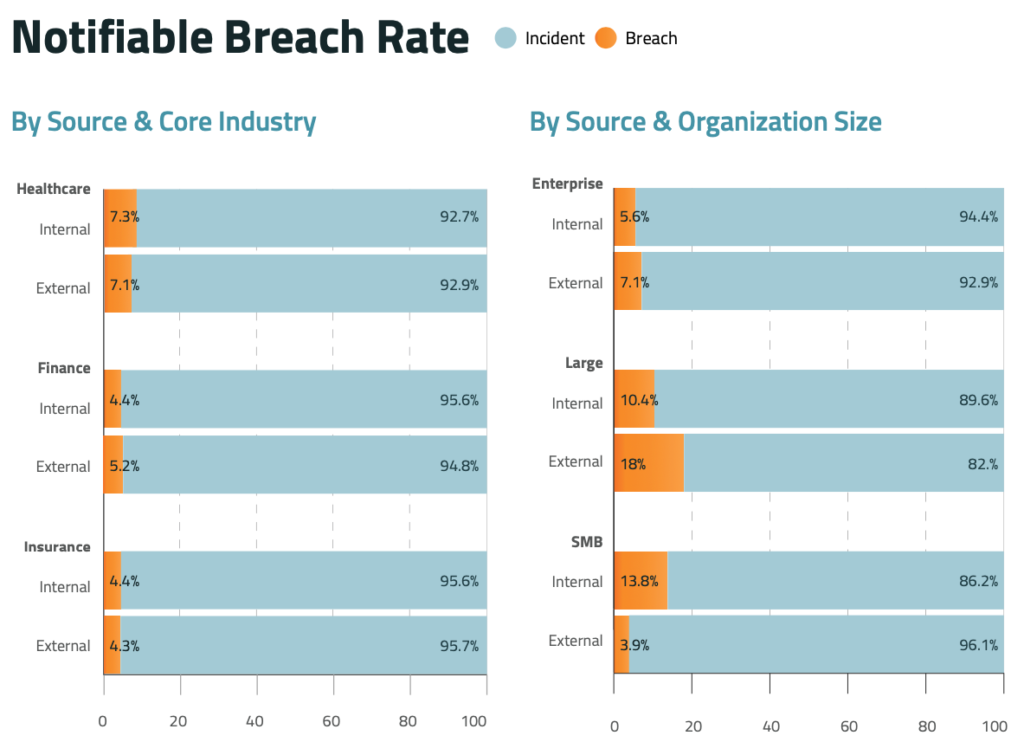
These benchmark figures provide a baseline for evaluating how your organization is doing on notification. If your notification rate differs significantly from the overall figures or the figures for your industry, it can indicate a problem.
Finding the Cause
Notification decisions depend on a lot of factors of risk assessment, so if your numbers are far from the average, it’s important to determine why. Here are some possible causes that your metrics might reveal:
- Data security and privacy practices: Maybe you really do have more notifiable incidents than the average organization. If so, do your metrics indicate where in the organization these incidents are coming from and where you have a gap. Are there data sets that should be better protected? Are there poor work practices that could be corrected with privacy training?
- Over-reporting or under-reporting: Is your staff going a little crazy in reporting anything that might be an incident? In sessions with The Privacy Collective, several of our panelists have mentioned temporary spikes in incident reports after privacy training, when staff is hyper-aware of potential issues. (Vigilance is good, but incident response takes time and resources, so there is a happy medium.) Conversely, is your staff under-reporting potential incidents, so that you learn about problems only after customers report them? If you’re mostly learning about incidents that are visible to customers, a higher percentage of those are likely to be notifiable.
- Issues with incident assessment: Is your incident response process leading to over- or under-reporting? For example, as regulatory notification deadlines have tightened (in some cases to as little as 72 hours from discovery) it has put tremendous pressure on the investigation and assessment phases of incident management. In response, some organizations tend to err on the side of notification rather than risk a decision not to notify when an investigation is incomplete. On the flip side, if an organization is struggling to keep up with new regulations and guidance, it may overlook some required notifications.
- Risk tolerance: Notification decisions need to be based on your organization’s unique needs and circumstances. So, your organization may simply have a higher or lower risk tolerance than average, which is reflected in your notification rate. That’s fine as long as your notification decisions are well-documented and consistent, in case regulators have questions.
The 7% Solution
In general, an incident notification rate below 7% is a good indicator that your organization’s data security and privacy practices are working, your incident response process is well-tuned, and you’re not putting the business at risk by over- or under-reporting. The keys to achieving this goal are:
- An automated multi-factor incident risk assessment to ensure the consistency and objectivity of your notification decisions
- An automated workflow that speeds data gathering and ensures that all relevant departments have input to an incident report
- Tools that automatically generate needed documentation about incident details, risk assessment, and notification criteria
- A dashboard that provides a high-level view of the incident response process and metrics
- A consistent review process that compares your organization’s metrics over time and against industry benchmarks to pinpoint problems, areas for improvement, and progress
Making the right choices about notification will not only protect your organization, its customers, and future business, it can also help your privacy team justify the resources and budget you need. If you can show that you’re saving money by balancing the risks of under-notification with the potential costs of over-notification, you have answered the million-dollar question. And that’s priceless!
[vc_column][vc_cta h2=”Read the 2022 Privacy Incident Benchmark Report” add_button=”right” btn_title=”Read Now” btn_color=”success” btn_link=”url:https%3A%2F%2Fwww.radarfirst.com%2Fresources/2022-privacy-incident-benchmark-report%2F|title:Read%20Now|target:_blank”] Read the report to learn more about industry benchmarks and incident management best practices. [/vc_cta]

Let’s Get Started
Trusted by leading organizations, RadarFirst enables teams to manage incidents with speed, consistency, and defensibility by standardizing how incidents are captured, assessed, and actioned.


