- People, process, technology: the three-legged stool of functioning Privacy
- 3 essentials for successful incident response risk assessment
- Guilty until proven innocent: do you trust your incident response process?
Read more below.
![Easing Today’s Incident Response [IAPP Webinar] | RadarFirst](/migration-images/uploads/2021/06/Easing-Todays-Incident-Response-IAPP-Webinar.png) Future-Proofing Compliance for Increasingly Complex Privacy Regulation
Future-Proofing Compliance for Increasingly Complex Privacy Regulation
Managing privacy and security incidents in an ever-changing risk and breach notification environment requires a forward-thinking, operationalized incident response program.
Are your processes scalable? Will you be ready when new regulations hit? How can you future-proof your privacy program?
It may seem daunting for organizations to manage the requirements of today’s incident response processes — let alone plan for inevitable incidents that are yet to come. If you need insights and best practices that can go a long way in helping privacy professionals improve their processes and make good data-driven decisions today — and in the future.
In the latest IAPP webinar, Future-Proof Compliance with Breach Notification Regulations — part of the IAPP Global Privacy Summit Online 2021 web series — Mahmood Sher-Jan, CEO and founder, RadarFirst, and Tim Smith, CIPP/US, VP, CPO, Unum Group, share real-world essentials for operational success and actions for improvement across each stage of the incident response lifecycle.
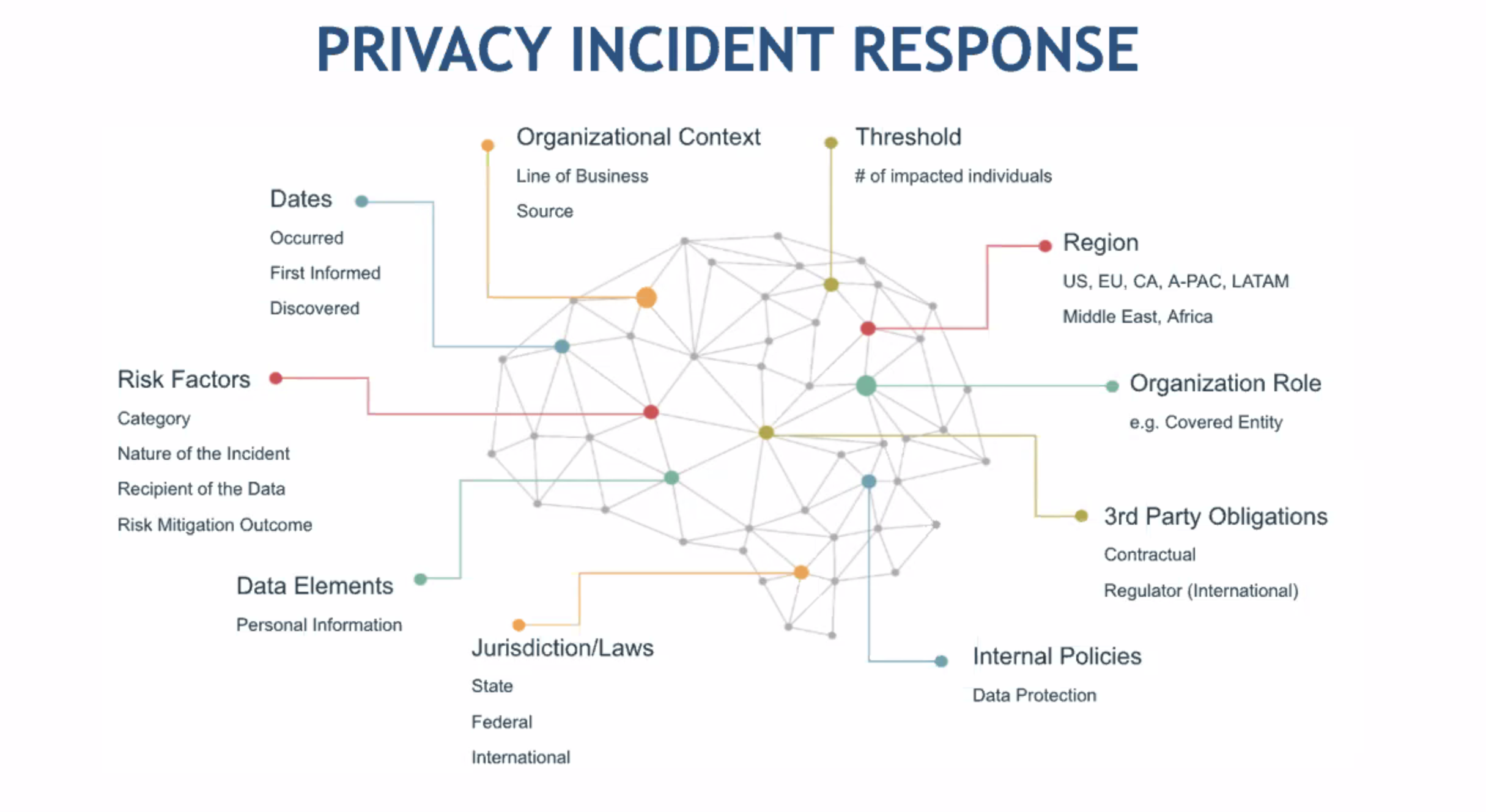
Getting a Handle on the Facts
When analyzing a privacy incident, there are many facts to consider during assessment: dates when the incident occurred, your organization’s role, risk factors, data elements, the threshold of affected individuals, organizational context, region, jurisdiction laws, internal policies, third-party obligations. These facts are critical and can determine whether or not an incident is a breach and if so if an organization needs to notify. People tend to get caught up in the noise of the incident versus the risk factors.
Fact-gathering is time-intensive. Having systems and operational capabilities in place will greatly reduce the time spent. “Having purpose-built capabilities to operationalize the process is really important,” recommends Sher-Jan. Adds Smith,
 “I call it people, process, and technology…it’s a three-legged stool and all three of those have to be functioning…because at the end of the day, judgment is involved. There has to be a technology that supports consistency in decision-making.”
“I call it people, process, and technology…it’s a three-legged stool and all three of those have to be functioning…because at the end of the day, judgment is involved. There has to be a technology that supports consistency in decision-making.”
 Three Essentials for Successful Incident Risk Assessment
Three Essentials for Successful Incident Risk Assessment
Your biggest decision in incident response is the incident risk assessment. How an organization assesses a privacy incident is critical. “Notification is a critical piece of the process because so much rides on it,” comments Sher-Jan. You don’t want to over-notify, you don’t want to under-notify and when you notify, you want to make sure that your notification is in compliance with the data privacy rules and regulations. Three risk assessment essentials:
- Base your risk assessment on complete, up-to-date regulations and jurisdictions, as well as contractual obligations
- A consistent and defensible risk assessment methodology to quantify risk of harm to individuals and the organization
- Document your decision criteria and the risk assessment results for regulatory, analysis, and/or legal needs
Operationalizing the incident risk assessment is where Radar fits in, with built-in, intelligent automation to give you triggers of what you should look for and prioritize. When describing Radar, Sher-Jan explains, “It’s not about building a self-driving vehicle, but creating the engine for those who are driving the vehicle.”
Guilty Until Proven Innocent
In the privacy incident management process, “We’re all guilty until we prove ourselves innocent,” says Sher-Jan. You prove yourself innocent by having a demonstrable risk assessment that indicates that the incident did not rise to that threshold of notification. A possible silver lining when assessing risks: over 98% of privacy incidents are non-malicious, based on findings from our 2021 Privacy Incident Benchmark Report.
“The world is getting more complex and privacy officers are getting stretched very thin and [in] a lot of directions — we need to really have trust and confidence in our people, our process, and our technology,” states Smith. “Compliance and incident reporting is so critically important, having an incident process…that you trust is…even more critical in this day and age.” Concurs Sher-Jan, “There’s a lot at stake here because you’re making decisions whether to notify or not and that’s a risk for the business if you’re wrong, or inconsistent.”
Listen to the on-demand presentation, Future-Proof Compliance with Breach Notification Regulations, to learn more about incident data and benchmarking insights, how privacy professionals can improve incident response processes, and take measures toward mitigating risks and future-proofing compliance.

