Key Takeaways IAPP Webinar: Privacy Incident Management Simplified

Jump to Section
In case you missed our latest session on simplifying incident management, we’ve got you covered. Continue reading for the key takeaways from the event.
Here’s What You Missed
- Time is a risk multiplier
- Collaboration and practice are key to simplifying incident management
- Embed privacy by design to accelerate maturity
- Benefits of reporting visibility
According to Gartner, decision intelligence is the integration of data analytics, automation and AI to create platforms to support, augment and automate decisions.
Privacy and Security teams are expected to make better decisions faster – allowing for scalability and predictability.
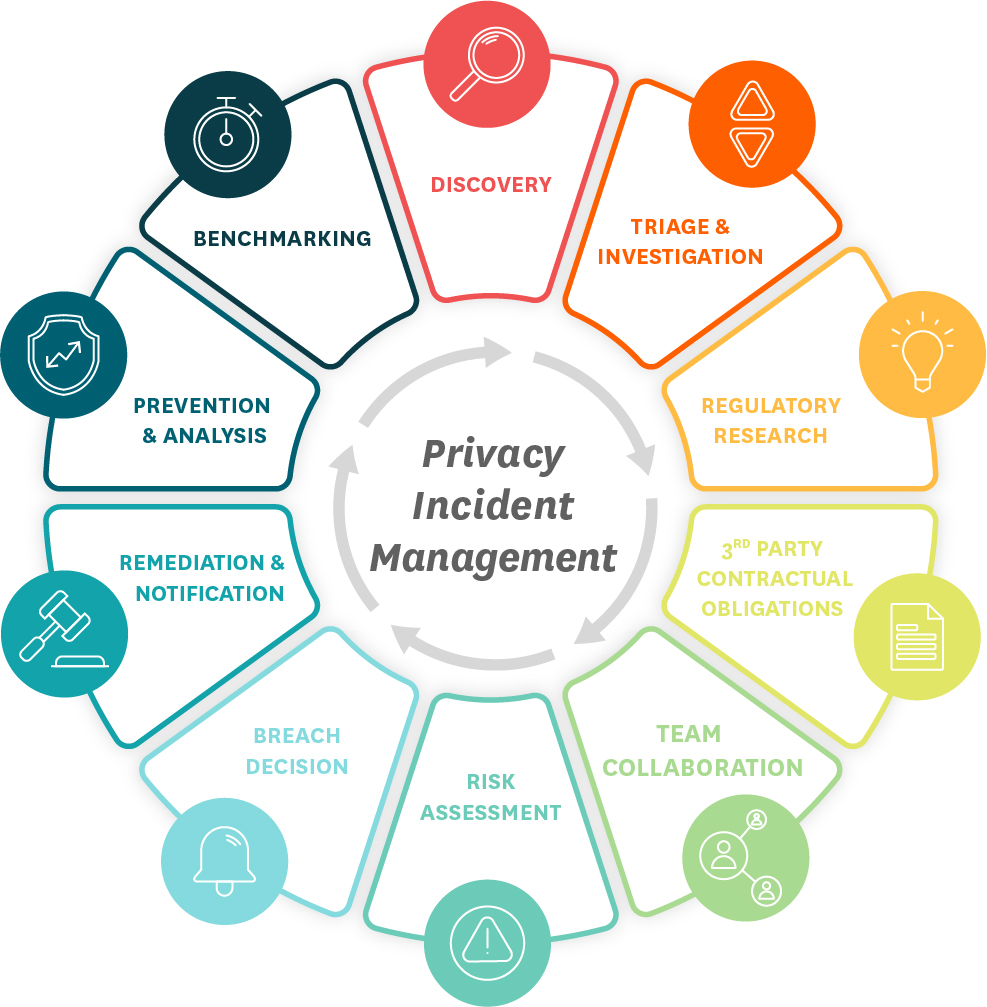
Based on our experience assessing hundreds of thousands of privacy incidents over the years, we believe that the incident lifecycle is best captured by the following ten stages.
These critical stages of privacy incident management are interconnected business tasks that must be acted upon every time a trust incident occurs. Of course, depending on the nature of the incident, some will require more attention than others.
We were joined by two healthcare industry experts who shared thoughtful insights into how they are simplifying incident management with these business functions.
Time is a Risk Multiplier
An incident is never linear. It overlaps within different stages and often requires you to jump back to a previous stage with new information.
“Oftentimes we have less than 24 hours to give notice. Sometimes it’s a business day, sometimes it’s three, and so [the ten stages process] becomes our de facto gold standard and it really helps us to get motivated, mobilize, and organize.” – VP of Regulatory Strategic Development at National Health Services Organization
Time is not your friend. In fact, we think of time as a risk multiplier – as more time passes, the chances of an incident becoming a higher risk of harm to the individuals that were impacted increases exponentially.
IBM tells us the average time from discovery to containment of a data breach is 277 days.
The RadarFirst 2022 Privacy Incident Benchmark Report captures an average time of 25-58 days (1-2 months) from occurrence to the first risk of harm assessment.
Disadvantages of manual processes
One of the panelists shared an example of how time can become a risk multiplier:
“Time is of the essence. The average time it takes from discovery to risk assessment is 1-2 months – and the majority of that time is often spent in determining what the impacts are and to whom. If you don’t know what the true impacts are (the facts), such as who and what personal information was involved, and where the individuals reside or live, it makes it virtually impossible to perform an accurate regulatory assessment. Combine manual discovery or determination with a manual process to determine regulatory impacts, and depending upon the complexity and size of the event, you have another month or so of time working against you.
Attorneys typically spend the majority of their time in a privacy event chasing down the latest data breach laws and requirements – which let’s be honest, is no small effort. An automated approach that will provide attorneys a first glance at notification requirements by jurisdiction (including individual and agency requirements), yet allows for the decision making to be held with the Privacy Officer and/or Privacy Attorney, would save time and create opportunity for the attorneys to work on other critical legal risks for the organization.”
A considerable amount of time is spent triaging an incident, which can be costly both to operations and reputation.
One of the biggest hidden risks is to third-party relationships though contractual obligations to notify. These third-party notification obligations often are in hours or days, as opposed to weeks or months, adding to the pressure.
When you’re up against the clock, mistakes can be made. Inconsistent decision-making is often to blame.
The risks of over- and under-notification
When notification decisions are made inconsistently, your organization runs the risk of over- and under-notification.
Over-notification typically happens when departments apply the most rigorous standard as precaution. Over-notification carries risks to brand reputation and can be a cause of customer and partner fatigue – leading to a disengaged stakeholder community.
Under-notification can be seen as a lack of transparency and can quickly deteriorate customer trust. It also carries the risk of hefty fines or penalties and jeopardizes trust with regulators and investors. The potential cost of losing trust far outweighs the benefit of actively building it.
An incident is a disruptor to business. In most cases, it causes panic, defensiveness, and certainly anxiety as your team works against the clock. Having the right tools to execute your plan is critical – your team can deconstruct incident management into strategic steps while prioritizing organizational goals and objectives.
Collaboration and practice are key to simplifying incident management
Having a compliant, centralized process brings all departments and individuals to the same table.
“There is no such thing as managing a privacy event alone – a bright, young attorney once told me, ‘It’s important to remember that while you may be the head of Privacy, you are not the head of the company and are not designed to be alone in the decision making process – there are others that have skill sets and knowledge in specific areas that are key to leverage’. Yes, there is definitely a need to collaborate across departments for this purpose alone, but also because we, in Privacy, are so typically challenged with resources. It’s critical to have incident response plans that integrate with other departments, with assigned roles and responsibilities. An end-to-end incident management process requires many people.” – Data Privacy Officer, HIPAA Privacy Officer at humanitarian aid organization
Sometimes, you may find there are too many cooks in the kitchen. This is why it’s important to have an incident management process in place. You must practice your plan with all involved stakeholders so everyone is aware of their responsibility.
Lessons from Remote Work
The way teams collaborate changed significantly due to remote work. It has led to an increased reliance on digital tools.
One benefit from remote work is a greater ability to reduce information silos and retain institutional knowledge. Using systems or applications to help with privacy operations can provide support, but they also provide consistency in approach.
Without a digital solution in place, onboarding for privacy teams took months. We heard from the panelists that with a digital solution, there was a much shorter learning curve and it only took weeks to get a new hire up to speed.
Our panelists continued to reflect on simplifying incident management with digital tools, “It made us more nimble at remote communication. I believe it also changed our teammates’ thinking from ‘their files’ to ‘our shared information.’”
Practice makes perfect
Creating shared goals and metrics across departments enables better collaboration to resolve incidents quickly and accurately. One way to start simplifying incident management is with a cross-departmental response plan:
- Know the objectives of the plan and who should be engaged
- Include a high-level process map that’s easy to follow
- Clarify breach criteria and definitions to make sure there is clear and consistent understanding
- Define when and who to escalate required incidents
- Allow for discussion on mitigation and recovery avenues
- Make sure the incident response plan is tested and well-understood in advance
- Build sub-playbooks for event types to accelerate resolution
- If you aren’t ready to build a full plan, start with checklist first and then evolve as you learn more
Once your plan is finalized, use that plan in tabletop exercises. You’ll want to create that muscle memory, so everyone involved knows how to move through the process.
Make sure to receive buy-in from leadership and also document your workflow for specific incidents.
Embed privacy by design to accelerate maturity
Your privacy program is continuously developing as the privacy landscape evolves.
Mistakes will happen and we know that human error remains the number one cause of incidents. Finding a three-dimensional way people can absorb privacy requirements and what it means to them in their role is extremely helpful. Training will need to be a continued effort in order to mitigate future risk and threats.
Embedding privacy by design is the next step in maturity. Leveraging process automation for incident management allows privacy teams to focus on larger enterprise initiatives. Privacy becomes a part of the design process for new products, helping to prevent future incidents.
Benefits of reporting visibility
Metrics tell a story – good or bad. This data can help build a business case for additional resources or technology. Even less mature privacy programs need some sort of reporting – to demonstrate in a quantitative way how well the program is doing.
Metrics help identify the root cause of incidents so that your team can better understand the specific areas that need assistance.
You can’t always wait for leadership to ask you for metrics and for visibility into reporting. Sharing data from your privacy program can illustrate how complex the privacy landscape has become and can also quantify how privacy drives value for the business (as opposed to being just a compliance requirement).
The panelists shared that generating reports in the past without an intelligent tool was very time consuming, taking hours on end. Now they can generate full reports for the board-level executives within seconds.
Analysis and benchmarking in RadarFirst allows you to track key performance indicators for continuous privacy program improvement.
With benchmarking specifically, remember to be mindful of what you’re comparing, and make sure it’s an “apples to apples kind of comparison,” as highlighted by one of our panelists.
Using data to accelerate maturity will help speed time to incident resolution.
Automation is no longer “a nice to have”
We know the clock starts ticking as soon as an incident occurs. What truly matters is how quickly your team can move through all ten stages of the incident lifecycle. That speed and accuracy will indicate your organization’s overall privacy maturity.
Our data-driven world has produced increasing regulation which creates an exponential challenge for businesses. Technology automation (or augmentation) is the only capability that can scale to meet this challenge.
[vc_column][vc_cta h2=”Watch the Full Webinar On-Demand” add_button=”right” btn_title=”Watch Now” btn_color=”success” btn_link=”url:https%3A%2F%2Fwww.radarfirst.com/resources/privacy-incident-management-simplified/%2F|title:Watch%20Now|target:_blank”] Interested in learning more? We’ve added the full webinar to our resource library for you to watch at your leisure. [/vc_cta]

Let’s Get Started
Trusted by leading organizations, RadarFirst enables teams to manage incidents with speed, consistency, and defensibility by standardizing how incidents are captured, assessed, and actioned.